Know Your Security Posture Before Your Customer Asks
Develomentor engagements include continuous security monitoring via our partner Aikido — so you walk into due diligence, SOC 2, and customer reviews with real answers.
Talk to Develomentor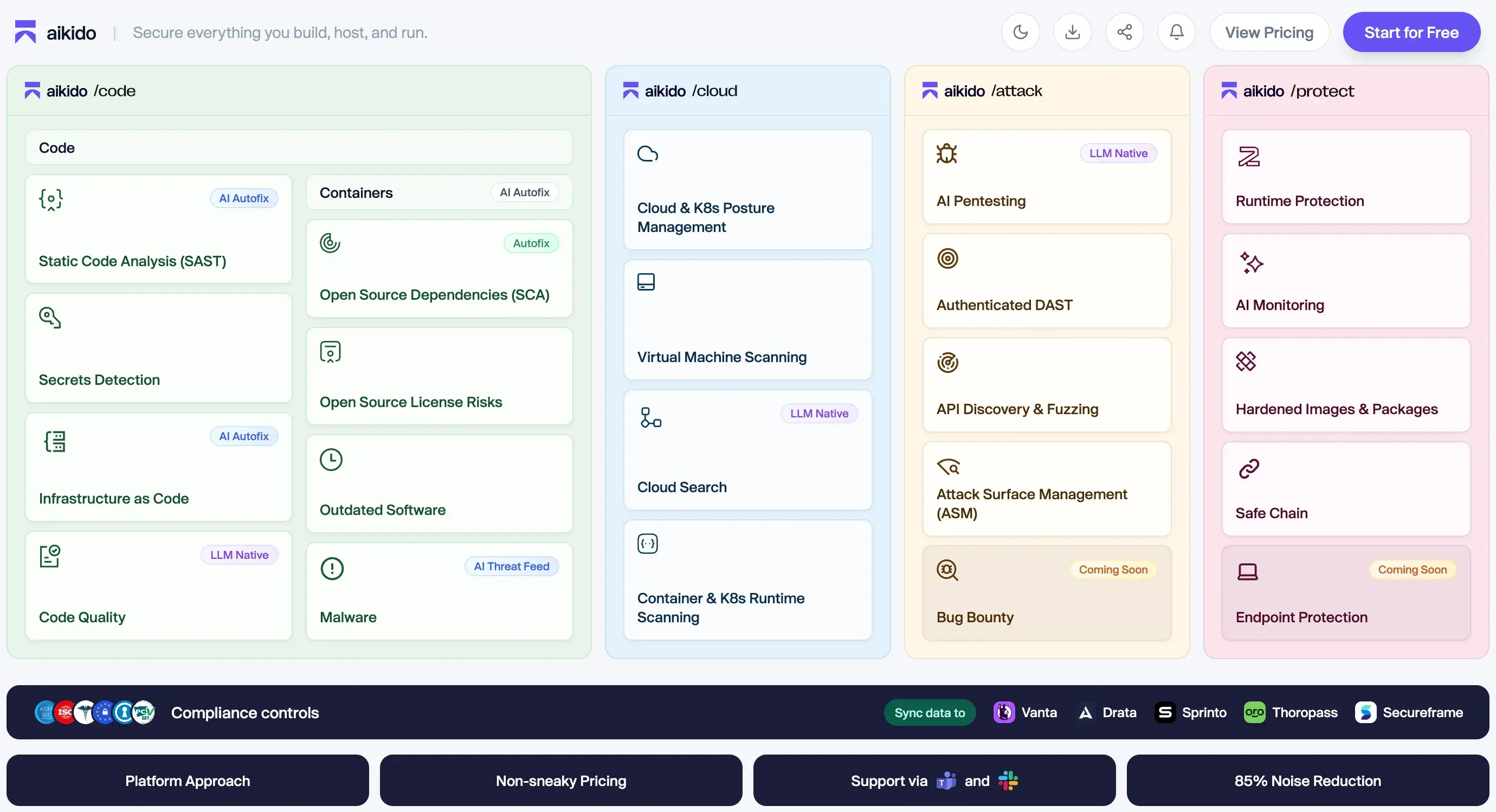
If Your App Is in Production, Security is Not Optional
If you have a production application facing the public internet and you cannot clearly answer how it is secured, Develomentor will not take the engagement without an Aikido Security license in place. That is a rule, not a preference — and our partnership means you do not have to source it, scope it, or fund a separate vendor relationship to get it. The companies we work with handle sensitive customer, financial, and operational data; getting security right from day one is materially cheaper, faster, and more defensible than retrofitting it later.
Aikido gives us one platform that continuously scans your code, open-source dependencies, cloud configuration, containers, and running applications. You do not need to read the scan reports. We translate what matters into business priorities, fix what is urgent, and put development procedures in place so new risk does not pile back up. Clients tell us the same thing: Aikido made security concrete and actionable for the first time.
See What We Would Find in Your StackWhat We Typically Find in the First 5 Days
Aikido is deployed during discovery. Findings start landing the same day we get access to your code and cloud. Here is what comes back from real engagements — and what each one means for your business.
-
Outdated dependencies with known, exploited CVEs — 80–90% of engagements
Your team is not careless. They are busy. Meanwhile, public CVE databases are an attacker's shopping list. Aikido names the exact library and exploit path, turning "we should probably patch" into a decision any executive can make in under a minute.
-
SQL injection vectors from unsanitized inputs — 30–40% of engagements
One overlooked input field is enough for an attacker to pull your customer database. This is the classic path from "small oversight" to breach notification letter.
-
Misconfigured cloud settings and exposed storage — 10–20% of engagements
Overprivileged IAM users, loose firewall rules, public S3 buckets. None of these look like a bug in your app. All of them can leak sensitive data to anyone who knows where to look.
-
Plaintext secrets committed to code — 10–20% of engagements
API tokens, database passwords, .env files in the repository. If your code is in GitHub and your keys are in your code, assume they are already public.
The surprise is never the individual finding. It is how fragile the software supply chain turns out to be — and how quickly that becomes manageable once you can actually see it.
What This Looks Like in Practice
FinTech startup, pre-launch
Purchased software from a prior vendor carried critical-severity vulnerabilities across the full stack and cloud deployment. Aikido surfaced all of it within hours and gave the team a concrete launch roadmap — not a vague "needs a security review." The head of product understood immediately: this can not be deferred. Today, Aikido's Zen runtime firewall protects the production application handling their clients' sensitive investment data and the dev team has clear, easy to follow processes in place for dealing with security.
Strategy consulting firm, going to market
Custom software built by a low-cost outsourced firm was days away from going live with clients whose data was anything but low-stakes. Aikido flagged compromised libraries and SQL injection paths immediately. Limited developer hours went to the issues that actually mattered for passing client IT security reviews — not a generic wishlist.
Small business, acquisition
A strategic acquirer ran technical due diligence on one of our clients. Aikido findings and documented remediation history served as concrete evidence of a proactive security posture. The buyer walked into the deal with confidence instead of a question mark — which is exactly what you want when the wire is about to move.
"Develomentor plus Aikido Security enabled us to confidently launch our new product offering, containing complex and sensitive data, into the market."
Why Aikido, Not the Usual Suspects
We evaluated per-seat scanners, open-source stacks, and enterprise platforms against the companies we actually work with. Aikido was the best fit. Here is what separated it.
After year one, clients can continue the subscription through Develomentor at a reduced rate even without an active Develomentor engagement. Security is not a one-time event.
See Exactly What Is Exposed in a Stack Like Yours
Schedule a 30-minute security risk walkthrough. We will show you Aikido running against a realistic application, walk through the findings typical in a codebase like yours, and answer the security questions your board, buyers, or investors are about to ask.
Schedule the WalkthroughReady to talk?
Tell us where you are and what decisions you are facing. We will get back to you within one business day.